Could you please give me an example, how do I decode received payload(that one I see in frame logs)? Of course I know all the key.
For this you can use the https://github.com/brocaar/lorawan library (Go).
Just decrypting a FRMPayload:
https://godoc.org/github.com/brocaar/lorawan#EncryptFRMPayload
To decode the full PHYPayload:
https://godoc.org/github.com/brocaar/lorawan#example-PHYPayload–Decode
I’m not familiar to the Go. Is there are any other ways to decode the message? I’ll give you an example for what I need it.
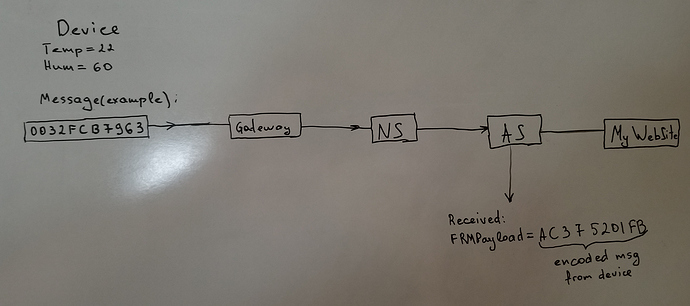
I assume that information encrypted by the device or NS. So I need this message (1) to have on MyWebsite, or in DB. Because I’ll know that lets say 0032=tempreture identifier, FC - temperature value. So I just need to have that message stored in DB. Where do I need to have code for decrypting? on the AS or on MyWebSite. MyWebsite is running on the Python base with MySQL.
What ways you can recommend for me to do this?
Thank you, @brocaar I appreciate your help.
Hello Oleg,
I am not addressed in your post, but still I hope you don’t mind my comments…
As I wrote before, I have a cloud server (a VM machine from arubacloud) running loraserver/lora-app-server/mosquitto/redis (and mysql/apache) and a php based service to move MQTT data into mysql. In this configuration, the PHP script subscribes to the MQTT broker for “application” messages. Once an “application” message is published on the MQTT broker, the PHP script decodes and stores the data on a MySQL table (actually several tables, because I need some more statistics about the end nodes). Of course you can use Python instead of PHP to write the service that decodes and moves the MQTT messages to MySQL. You can find lots of examples of this on the Internet.
Displaying the data on the website (running under Apache) is done by a PHP / JavaScript based webpage.
I hope my post helps you.
Regards,
In that case, don’t look at the frame-log. In the latest release I’ve added a note to it that these are the raw and encrypted frames and meant for debugging purposes (e.g. when you have issues with sending / receiving mac-commands).
To receive the plaintext payloads (thus the unencrypted 0032FC.... payload), please look at: https://docs.loraserver.io/lora-app-server/integrate/data/. Alternatively, you could setup a HTTP integration so that LoRa App Server will POST to your Python application.
Hi @glederer007,
Thank you for your answer, that actually make good sense to me. I think I will implement this with python only one question is a decoding data. But I think @brocaar referenced link that I believe will be the clue for me. As I understood, if I will subscribe to MQTT topic as in examples I will see the decoded data.
Thank you guys! That is really helpful!
Best regards,
Oleg Somov
Hi Orne,
Finally can do some work on this. This is a bit confusing for me, so if you can give me some hint over here, it would be great.
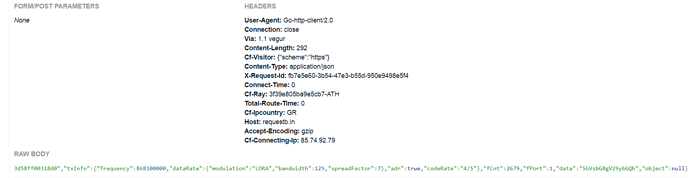
I’ve followed your instructions, subscribed to the “application/#” and I’m receiving messages:
{"frequency":902700000,"dataRate":{"modulation":"LORA","bandwidth":125,"spreadFactor":8},"adr":true,"codeRate":"4/5"},"fCnt":4,"fPort":1,"data":"qg=="}
I dropped like half of message(needless for question). The question is - I’m receiving “gg==” which is not what i sent from device. I wonder how to make it be the way I sent it. Is it the only way to do that is do kinda"decode.base64"? If yes, so why I can’t get any result from using WebApps to decode message?
Thank you,
Oleg Somov
Is it the only way to do that is do kinda"decode.base64"? If yes, so why I can’t get any result from using WebApps to decode message?
I don’t understand your question fully, but the way to decode base64 is for example: Go Playground - The Go Programming Language (both to raw bytes and re-encode to hex).
Thank for the answer, @brocaar,
Yeah, I understood that already, got my message.
BTW: Do you have some documentation about encryption on the way from device to AS? I mean, how is it happening on your server.
Best regards,
Oleg Somov
That is used for both encryption and decryption of the FRMPayload. For the documentation behind this implementation, please refer to the LoRaWAN specification: LoRaWAN for Developers - LoRa Alliance®.
Hello @brocaar and @Oleg_Somov.
After many time of search, this post is exactly what i was searched in order to understand the way that AS encode the message, which sent from my node-device to loraserver,so that i will be able to decode it in my way (manually) creating a new API (using Python for example.)
But first, would be essentially to understand the above issue.
Using a HTTP integration, i receive a message, which give me data as:
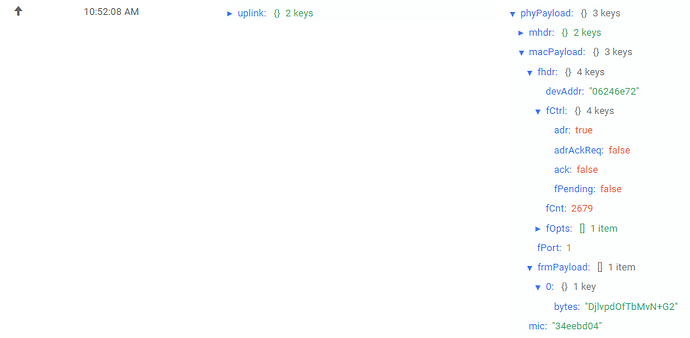
In lora-server, i also see Live Frame Logs and in phyPayload i receive:
My question is: why this difference in data value? it supposed that i receive a phyPayload, which is encrypted in the same way. My device message is a sequence of bytes, that is encrypted as you mentioned in https://godoc.org/github.com/brocaar/lorawan#EncryptFRMPayload and then i try to decode it back.
Your advice will be essential.
The difference is that the first screenshot shows the decrypted frame (e.g. decrypted with the AppSKey). The second screenshot is the raw PHYPayload without any form of decryption (e.g. how somebody else would see it when putting a gateway near your device). See the live frame-logs feature as a Wireshark kind of tool for LoRaWAN.
Thanks for the reply @orne! So, the depcrypted frame is decoded (using base64) in text form, as it supposed to show in first screenshot, in “object” field, after using Custom Javascript codec functions, right?
Mosquitto_sub suppose to be the same as HTTP Integration or Live Packet Frame?
Hello Broccar,
I have my applicaton subscribed to MQTT but before that I have made some tests using only live frame logs and lost some very important data.
I am trying to retrieve that data passed from a device through the live frame log of the gateway, the gateway frame log is the only I have.
The Live Frame log of an gateway contains the data sent by the device in some kind of encrypted form?
What is the technique used to encrypt and decrypt that data? Have not succeded in AES128
By having the keys is it possible to convert the frmPayload into the bytes sent by the device?
Seems to me that the frmpayload is in the middle of the data worklad, neither is the original PhyPayload to use and get my payload nor is the data I want and I have been trying to convert it for a while now but the go library have not helped much me so far.
I have searched documentation in https://www.lora-alliance.org/for-developers but they do not have an pdf to download or maybe the website has changed the docs.
If you could help me I would realy apreciate it.
hi @brocaar, how can I decode the gateway payload from topic such as gateway.{gateway-id}.event.stats? I can read the payload from device that are coming from topic such application.{application-id}.device.{device-id}.rx but the payload from gateway seems like garbage and when I convert it to Hex it becomes something like this 76f1c9d7bdb5f38d36644cfe58. Could you please help me read it?
Hi @sherwin I am facing same problem. Did you get your answer? If yes then please share with me. Thanks!